How Fraudsters Bypass MFA to Get into Banks, Brokers and Crypto Wallets
 Alex McConnell, Cybersecurity Content Specialist
Alex McConnell, Cybersecurity Content Specialist
10 minutes read
Passwords are dying as a sole security measure, particularly within financial services.
It is widely expected (and in the UK, mandatory) that any institution responsible for finances, from banks to brokers and even crypto wallets, should be implementing multi factor authentication (MFA) to prevent fraudsters gaining access to accounts using automated attacks, even if they know the user’s password.
This blog post outlines several MFA bypass techniques attackers have developed to carry out account takeover attacks on financial services organizations.
What is MFA (multi factor authentication)?
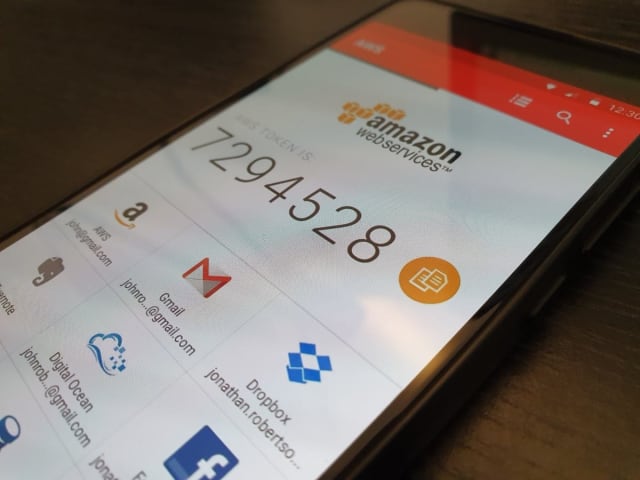
MFA – or multi factor authentication – is a security measure designed to prevent unauthorized access to accounts, even when the attacker has the user’s password. Any login requires an MFA access code (like a one time password) generated on a device belonging to the account owner using a third party MFA provider app like Google Authenticator or Authy. In theory only the account owner can access the code and log in, even if their credentials are compromised by a bad actor.
2FA (two factor authentication) is a type of MFA that uses exactly two factors for login (usually credentials plus a device). The second factor could be a code sent via a text message or to an app. All 2FA is a form of MFA, but not all MFA is two factor authentication as more factors could be required.
How is cryptocurrency stolen?
The nature of blockchain currencies makes them highly susceptible to fraudulent activity. Transactions are difficult if not impossible to trace, making it easy for adversaries to get away with stealing large amounts of virtual cash undetected.
Between October 2020 and March 2021, 7,000 people reported a collective $80 million stolen in cryptocurrency – 12 times the number of reports than in the same period the previous year, with over 1,000% more money stolen.
Here are some of the most prevalent types of cryptocurrency fraud:
Guru cons and investment scams
As people are drawn into the hype around making money through crypto investments, inevitably so-called “crypto gurus” have found a niche selling advice to newcomers. Sadly, fraudsters have taken advantage of the situation. In one scam, more than $2 million was stolen by fraudsters impersonating cryptocurrency advocate Elon Musk. These con artists promised to multiply the victims’ investments, but instead stole the money with no hope of retrieval.
Romance scams
The difficulty in tracing transactions makes cryptocurrency a perfect tool for romance scammers who manipulate their victims into transferring huge sums of cash. The FTC reports that over $185 million has been lost via cryptocurrency transactions in romance scams since 2021 – one in every three dollars lost to the scams overall.
Account takeover
Unlike traditional banking, crypto transactions are hard to reverse or trace. There is little support due to the decentralized nature of the currencies; password recovery mechanisms are less robust than traditional banks, and repatriating stolen accounts is harder as proving yourself to be the legitimate account owner is not straightforward.
These factors make cryptocurrency wallet fraud attractive to ATO attackers where risk and cost are low but potential rewards are extremely high.
Account takeover is still a major concern in financial services
Account takeover (ATO) is the holy grail of fraud attacks in financial services, handing criminals their victims’ financial assets on a platter. The risk of accounts being stolen affects both traditional banks as well as FinTechs and crypto wallets.
The first step in most attempts to gain access to bank accounts is credential stuffing. MFA is a way to stop attacks like credential stuffing.
How can credential stuffing give access to a user’s account?
First, the attacker acquires a list of credentials (username and password pairs), usually through some form of credential theft. This could either be a data leak from another site published on the dark web, or by buying ‘botnetted’ device fingerprints and session cookies from marketplaces like the Genesis Market.
If only part of credentials is obtained, attackers can use brute force to guess the password based on published lists.
Next, threat actors inject these credentials into the login pages of a targeted company to determine which ones are legitimate. This is usually done at great velocity and volume using bots to automate the process.
Some attacks make millions of login attempts within just a few hours, so even a small success rate at this scale can yield hundreds or thousands of accounts, which is a big win for criminals.
Any validated credentials can then be used for an account takeover attack. Once in, threat actors can access sensitive data, perform a password reset and completely control the user account, even transferring money elsewhere.
How to protect your crypto wallet from thieves
In cryptocurrency terms, your wallet’s private key is your money, so anyone who has access to it essentially has access to your funds. Private keys are frequently encrypted by a password so keeping both safe is essential.
Here are a few precautions you need to consider to secure your cryptocurrency.
Use multifactor authentication using an app
Multifactor authentication (MFA) is an additional step to protect accounts that may have their passwords compromised, adding an extra hoop for criminals to jump through. However, with an attractive reward inside your crypto wallet, there are ways around SMS verification as a form of MFA.
If an adversary knows your phone number along with other PII to get past security questions (often obtained through social engineering), they can fool your mobile network provider over the phone in an attack called phone porting. The network is persuaded to swap the victim’s SIM card to another phone, allowing the attacker to access SMS verification and clear MFA.
The solution is to use dedicated authenticator apps like Google Authenticator or Authy instead of just a phone number as multifactor authentication.
Use a strong, unique password, or even separate email addresses for each wallet
If an attacker gains access to one account, quite often they can access other accounts owned by the same person due to many people reusing the same passwords. This is unsurprising since the average person has 191 passwords to remember for their online accounts.
The way to protect against this is to always use a strong, unique password for every service. Password managers are an essential tool for this purpose, ensuring only strong passwords are generated and keeping them safe with one master password.
You must be extremely careful with any password storage you rely on, as there is no way to recover lost passwords for crypto wallets due to the decentralized nature of cryptocurrency.
You might also want to create a totally separate email address for each crypto wallet, so there is even less risk of losing access to your whole balance should one service be compromised.
Protect your private key with cold storage
Your public key is like an address others use to transfer money to your account, while you need your private key to send money to others. It’s essential to keep your private key away from prying eyes. Cold storage is one way to achieve this.
Cold storage of a private key involves physically writing down the key on a piece of paper, locking it away in a safe or deposit box, and erasing all digital traces of it. Just be extremely careful you don’t lose this physical copy or put it anywhere it can be lost, destroyed or stolen.
Use a hardware wallet
A similar tactic to cold storage of your private key is using a hardware (or cold) wallet. These are physical devices which cryptocurrency can be transferred onto, which are then kept offline, like withdrawing cash from an ATM and keeping it in a traditional wallet.
The advantage of doing this is it keeps your balance offline and safe from being withdrawn remotely by anyone else. But, as with a traditional wallet, theft is always possible, and if lost, the funds on the device will be irretrievable.
How can multi factor authentication stop credential stuffing and account takeover?
MFA is designed to stop ATO attacks by requiring more than just a password (usually something in the account owner’s physical possession) to validate a login, preventing automated attempts.
Unfortunately, attackers can bypass MFA security using a combination of bot and human intervention, either by sidestepping the need to use MFA for account access or using clever tricks to fool account owners into handing over MFA codes.
How do attackers bypass MFA?
Here are some common MFA bypass attack vectors:
Financial aggregator sites
APIs are a huge target for financial fraudsters, as the adoption of Open Banking API to meet PSD2 requirements opened a new attack vector.
APIs are exploitable via financial aggregator sites. Bank customers use services such as Mint, Plaid and Yodlee to manage their finances, aggregating accounts into a ‘single pane of glass’ view. These apps can access account information and even make changes using the bank’s API or a webapp, sometimes without requiring MFA.
A threat actor can perform credential stuffing attacks through a third-party financial aggregator app to bypass MFA controls.
Security questions and social engineering
Some banks make provisions in case their users lose the device used for MFA, or don’t have access to it for some reason. This is a way to bypass MFA using the bank’s own policies.
The most common method of verifying identity in this case is through security questions. Attackers use social engineering, which can be as simple as quickly looking at social media profiles, to gain answers to common security questions and access accounts without MFA.
Bots can therefore use credential stuffing to bypass MFA and instead answer security questions either by brute force or using publicly available data.
Phishing
MFA bypass attacks often run in parallel with phishing attacks. Phishing is a means to trick users into giving up sensitive information, such as passwords or information useful for passing security questions.
Phishing can also be used to extract codes generated by MFA apps from account owners.
Techniques include trying to convince an individual to visit a fake login page and input the MFA code. The threat actor might also email or phone an individual and impersonate their bank to ask for the MFA code. In this way, rather than bypass MFA, attackers gain access to MFA codes maliciously.
Man-in-the-middle
In a man-in-the-middle (MITM) attack, the threat actor positions themselves between the bank and the customer (often by using malware) and intercepts the messages between them. They can use this to acquire an MFA code, for example by linking to a fake page asking for the MFA code.
SIM swapping
SIM swapping entails intercepting text messages sent to a user’s phone number and having them sent to another handset. This is often done by calling up the user’s SIM provider and impersonating the customer using social engineering to pass security questions.
The threat actor then convinces the operator to swap the phone number to a new SIM card in the attacker’s possession. Once this is set up, the threat actor can use this phone number as the authentication factor to gain access to the user’s account.
Why can’t MFA completely stop bot attacks?
While we have presented a few ways fraudsters get around MFA defenses, it’s true that MFA is stronger than passwords alone, and is still likely to slow down attacks, force a degree of human intervention, or yield fewer stolen accounts.
However, because they can run at such high volumes, bots don’t need a very high success rate to be profitable. Banks are still at risk of having customer accounts stolen by bot attacks, even with MFA in place.
In essence, adding an extra layer of defense has forced criminals to become even more sophisticated in the ongoing cat and mouse chase between security experts and their adversaries.
Subscribe and stay updated
Insightful articles, data-driven research, and more cyber security focussed content to your inbox every week.
By registering, you confirm that you agree to Netacea's privacy policy.