Account Takeover
Stop malicious actors from seizing control of customer accounts.
Detect and mitigate even the most sophisticated threats with Netacea’s online fraud prevention solution. Our AI-powered fraud protection services can secure you against brute force attacks and attack vectors, reducing the risk of fraud from automated attacks.
Learn how Netacea helps you defeat:
Stop malicious actors from seizing control of customer accounts.
Detect and block automated card cracking, carding and enumeration attacks.
Stop attackers from brute forcing their way into your customers' accounts.
Halt attempts to create masses of accounts; damaging your business.
Prevent exploitation of new account bonuses and fake account creation.
Maintain the integrity of online sales and ensure goods go to real customers.
Prevent bots from stealing your marketing budget and skewing your analytics.
Identify and stop web scrapers that compromise your website.
Online fraud is rising rapidly, bad bots can now evolve faster than security teams can keep pace with, creating a significant burden and drain on your resources. Conventional fraud detection solutions are no longer adequate in providing timely, efficient or effective online fraud detection. Getting it wrong is costly, our research shows 3.6% of annual revenues are lost due to ineffective online fraud prevention.
Conventional bot management relies on signs like suspicious IP addresses and dubious user agents. Bad actors know this and readily adapt their methods to breach those defences, further increasing the risk of fraud. Our online fraud prevention solutions offer a more robust and automatic method of defense for online fraud detection that hackers can’t bypass.
By the time an attack has been uncovered, it’s usually already too late for both your business and the security of your customers or clients. The fraudster will have taken their spoils and moved onto their next victim before you were even aware they existed – that’s where our online fraud detection services come in.
Forrester, a leading research organization, identified Netacea as a Strong Performer in its 2022 evaluation of the bot management market.
Forrester has identified Netacea’s bot detection capability as the highest scoring of any vendor in its 2022 evaluation of the bot management market.

In April 2023, the Genesis Market was seized by the FBI working with 16 other countries. What does this mean for other sites selling stolen digital identities?

AI is a powerful tool for both good and bad. ChatGPT is a prime example that can be exploited to create malicious bots. How can we protect against this?
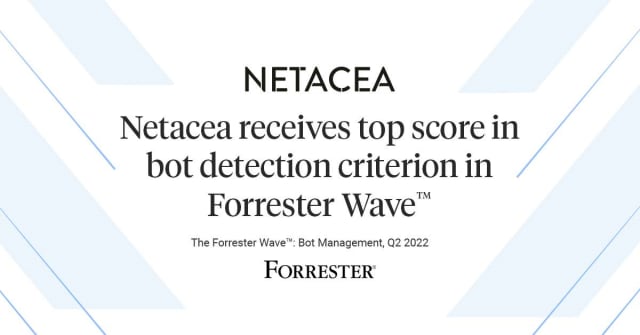
'"Netacea consistently punches above its weight in thought leadership and research." – The Forrester Wave™: Bot Management, Q2 2022 report. Find out why Netacea leads the pack.'